Abstract
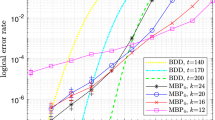
The discovery of holographic codes established a surprising connection between quantum error correction and the anti-de Sitter-conformal field theory correspondence. Recent technological progress in artificial quantum systems renders the experimental realization of such holographic codes now within reach. Formulating the hyperbolic pentagon code in terms of a stabilizer graph code, we give gate sequences that are tailored to systems with long-range interactions. We show how to obtain encoding and decoding circuits for the hyperbolic pentagon code, before focusing on a small instance of the holographic code on twelve qubits. Our approach allows to verify holographic properties by partial decoding operations, recovering bulk degrees of freedom from their nearby boundary.
Similar content being viewed by others
Introduction
Holography emerged as a key concept in high-energy physics, gravity, and quantum information. With the introduction of the anti-de Sitter-conformal field theory (AdS-CFT) correspondence by Maldacena1, holographic duality established a relation between two physical theories, one sitting in the bulk and the other sitting at the boundary of a hyperbolic space2,3. In an effort to understand this AdS-CFT correspondence further, geometrically arranged tensor networks arose as a useful tool, displaying unique entanglement properties4,5,6 This link between geometry and quantum entanglement led to recent efforts seeking an experimental realization of holography7,8,9,10. However, an experimental realization of the proposed tensor networks is challenging.
The hyperbolic pentagon code proposed by ref. 11, also known as HaPPY code, is today’s premier toy model for understanding holographic duality. It is composed of a tensor-network with absolutely maximally entangled states (also known as perfect tensors) as basic building blocks. This model exhibits several desired features such as a uniform bulk and an entanglement entropy constrained by the Ryu-Takayanagi formula12.
Despite recent theoretical investigations into the error-correcting capabilities of holographic codes13,14,15,16,17, experimental implementations have yet to come forward18. In this work we close the gap towards an experimental implementation and bring the stabilizer approach to holography19 to its logical conclusion by formulating it as a graph code. This opens up a path towards investigating AdS-CFT like models experimentally, making their unique partial recovery features accessible for current and upcoming quantum technologies.
Our framework yields a graph state from which we derive the gates necessary to encode, perform logical gates, and decode quantum information. Additionally, it exhibits the essential characteristic of holographic systems, that is the ability to recover a bulk region from its nearby boundary.
While challenging, our toy model can already be implemented with as few as 12 qubits, with experimental requirements that are within reach of current neutral atom platforms20, superconducting qubits21 and trapped ions experiments22.
Recent experimental efforts show the possibility to engineer long-range connectivity in neutral atom systems23,24, trapped ions25,26 and superconducting qubit platforms21. Depending on the platform the long-range interaction between the qubits is realized by coherently transporting the qubits or using a connecting bus.
In contrast to more common methods which require stabilizer measurements to prepare the logical zero state27, our approach reduces this task to a graph state preparation. For the trapped ions set up from28, the graph state fidelity is estimated higher than the fidelity of the state prepared via stabilizer measurements.
Results
Main contribution
We formulate the hyperbolic pentagon code introduced by Pastawski et al.11 in terms of its corresponding stabilizer graph code. This allows to derive the encoding and decoding gates, as well as the partial recovery operations that are required to demonstrate holography experimentally.
Our approach is based on three observations: first, by choosing stabilizer states as building blocks, the hyperbolic pentagon code can be written in stabilizer form19. Second, a stabilizer code which encodes k into n qubits can be represented as a graph code29, that is, a graph state on k + n systems. Third, the number and range of interactions of this graph can be optimized through local Clifford operations, significantly reducing the experimental requirements to prepare the code states.
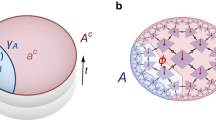
This procedure allows us to represent the hyperbolic pentagon code as a stabilizer graph code in a manner suitable for experimental implementation (c.f. Fig. 1). In addition, our method also provides the gates necessary to recover parts of the encoded bulk degrees of freedom from their nearby boundary, thus demonstrating holographic features.
A small instance of the hyperbolic pentagon (HaPPY) code11, represented as a graph state or graph code. This representation is obtained from mapping the tensor network to a stabilizer state and then finding an experimentally suitable local Clifford equivalent graph state. The entire construction can be described as a holographic graph code.
Following the method described above, we propose an experimental implementation of a small instance of the hyperbolic pentagon code on twelve qubits (c.f. Fig. 1). Through a stabilizer graph code representation, we provide the gates required to encode and decode four bulk qubits into twelve boundary qubits. In addition, we show how to demonstrate holographic features of the logical code states. We list the specific gates needed for a partial decoding operation which recovers two bulk degrees of freedom from their nearby five-qubit boundary.
This places the experimental implementation and certification of holographic systems within reach of current experimental high-connectivity platforms such as Rydberg atoms in optical tweezers, trapped ions, or cavity-coupled qubits. Specifically by using trapped-ion setup from28, we estimate a higher logical zero state fidelity with our method than with currently available ones27. We suggest as first step towards the implementation of the holographic pentagon code, the preparation of the logical zero state. It is noteworthy that our proposal is of a scale that can be compared against numerical simulations. The reader only interested in the experimental implementation can directly jump to A holographic model on 12 qubits.
Holographic code
A holographic code encodes k bulk qubits into n boundary qubits with n > k, such that any bulk region can be recovered from its nearby boundary. The bulk degrees of freedom live in the Hilbert space \({{{{\mathcal{H}}}}}_{{{{\mathcal{B}}}}}\) and host the message, whereas the code space \({{{\mathcal{C}}}}\) is a subspace of the boundary space \({{{{\mathcal{H}}}}}_{\partial {{{\mathcal{B}}}}}\). The encoding of the bulk into the boundary is mathematically defined by a norm-preserving linear map \({T}_{{{{\rm{H}}}}}:{{{{\mathcal{H}}}}}_{{{{\mathcal{B}}}}}\to {{{\mathcal{C}}}}\subset {{{{\mathcal{H}}}}}_{\partial {{{\mathcal{B}}}}}\), i.e., an isometry. The norm-preserving property of isometries can be written as \({T}_{{{{\rm{H}}}}}^{{\dagger} }{T}_{{{{\rm{H}}}}}={{\mathbb{1}}}_{{{{\mathcal{B}}}}}\). For our purposes the corresponding Hilbert spaces are \({{{{\mathcal{H}}}}}_{{{{\mathcal{B}}}}}={({{\mathbb{C}}}^{2})}^{\otimes k}\) and \({{{{\mathcal{H}}}}}_{\partial {{{\mathcal{B}}}}}={({{\mathbb{C}}}^{2})}^{\otimes n}\) but qudit Hilbert spaces are also possible. Then, the isometry can explicitly be written as
mapping each computational basis element \(\left\vert {i}_{1}\ldots {i}_{k}\right\rangle\) in \({{{{\mathcal{H}}}}}_{{{{\mathcal{B}}}}}\) to its corresponding logical state \(\vert {H}_{{i}_{1}\ldots {i}_{k}}\rangle\) in \({{{\mathcal{C}}}}\). Given the Pauli gates Xj, Yj, Zj acting on the j-th qubit in \({{{\mathcal{B}}}}\), the isometry TH can be used to find the logical gates, which act on \({{{\mathcal{C}}}}\) in the same way as Pauli gates on \({{{{\mathcal{H}}}}}_{{{{\mathcal{B}}}}}\).
By turning the bra vector acting on \({{{\mathcal{B}}}}\) into a ket, the isometry in Eq. (1) can be represented by an unnormalized quantum state
where we changed the order of the kets (bulk and boundary) for consistency with later sections. Therefore, the holographic code can be described by a state which we term holographic state. From Eq. (2) we see that \(\left\vert H\right\rangle\) is maximally entangled with respect to the bipartition \(\partial {{{\mathcal{B}}}}\) and \({{{\mathcal{B}}}}\), which we denote by \({{{\mathcal{B}}}}| \partial {{{\mathcal{B}}}}\). In reverse, each state of the form given in Eq. (2) induces an isometry. Specifically, absolutely maximally entangled (AME) states, often referred to as perfect tensors when the number of parties is even, are maximally entangled with respect to any bipartition.
An interesting way to construct a holographic code is via a tensor network that uses AME states as building blocks. Here we show how this holographic code can be understood as a graph code11,30. In a tensor network the tensors are connected by lines which correspond to index contractions. While contracting two AME states does not necessarily yield another AME state, the contraction is still an isometry. This fact can be directly seen from the tensor network representation of contracting two AME states. By assembling and contracting the tensors properly, one can construct a state that is maximally entangled across \({{{\mathcal{B}}}}| \partial {{{\mathcal{B}}}}\). Using such a maximally entangled state one can map bulk qubits to boundary qubits. Since we use AME states as building blocks, the isometry is decomposed into further smaller isometries. These smaller isometries allow us to recover bulk qubits from their nearby boundary qubits, making the code holographic.
The geometry of the tensor network determines how the decomposition of the isometry is performed and, therefore, which information can be recovered. In this article we consider the hyperbolic pentagon code that contains six-qubit AME states as building blocks11. This AME state was described first as GF(4)-hexacode in a seminal article by Calderbank et al.31 on the connection between classical and quantum stabilizer codes. The state was numerically rediscovered in ref. 32 and brought to graph state form in ref. 33. When the number of parties is even, such states are often referred to as perfect tensors. Figure 2a illustrates the recovery for a specific boundary region: given the boundary qubits on the partition ∂E, it is possible to recover the bulk qubits on E without using the qubits on ∂F.
The k bulk qubits (in red) are encoded into n boundary qubits (in gold). Each pentagon represents a six-qubit perfect tensor, also known as absolutely maximally entangled (AME) state. The geometry of the assembly makes the holographic state maximally entangled across \({{{\mathcal{B}}}}| \partial {{{\mathcal{B}}}}\). a shows a specific region of the bulk E which can be recovered by reading only the region ∂E of the boundary, where the cut γ is of size ∣γ∣ = 3. b shows a small instance of the code (red) which we propose to prepare experimentally.
An important characteristic of holographic codes is that the Ryu-Takayanagi formula holds12. Roughly speaking, given a boundary bipartition ∂E∣∂F and associated bulk regions E∣F, the Ryu-Takayanagi formula states that the entropy of the reduced state on ∂E is proportional to the length of the bulk geodesic that separates E and F, in addition to a bulk entropy term. For the holographic code considered here the formula can be stated as S(∂E) ∝ ∣γ∣ for encoded product states, where ∣γ∣ is the number of contracted indices in the tensor network that cross from the E to F (see Fig. 2b). Linked to this is the ability to perform a partial bulk reconstruction, recovering a part of the bulk from its nearby boundary, a property which can be tested experimentally and will be addressed in Partial decoding circuit.
The construction of holographic codes via tensor networks is well suited to visualize the geometrical aspect of the code. On the other hand the stabilizer formalism is highly efficient in determining encoding and decoding strategies and to obtain the logical states and gates. Hence, we will discuss in the following section the stabilizer formalism in order to apply it to the hyperbolic pentagon code.
Stabilizer states
An m-qubit stabilizer state is characterized by ℓ independent commuting operators gi that form the stabilizer S = 〈g1, …, gℓ〉, with ℓ ≤ m and \(-{\mathbb{1}}\,\notin \,S\). The gi are elements of the m-qubit Pauli group \({{{{\mathcal{P}}}}}^{m}\), which is formed by tensor products of Pauli matrices X, Y, Z and phases { ± 1, ± i}. Note however that the phases of the stabilizer elements are always real. A stabilizer state34,Section 10.5.1 can be written as
The state ϱ is proportional to a projector which acts on a subspace of dimension 2m−ℓ. When ℓ = m the state is pure.
A convenient way to represent a stabilizer state is through its check matrix. This is an ℓ × 2m matrix C = (A∣B) whose rows correspond to the ℓ generators. The matrix A accounts for the X-part and B for the Z-part of the generators: Aij = 1 if gi contains an X at position j, Bij = 1 if gi contains an Z at position j, Aij = Bij = 1 if there is a Y, and Aij = Bij = 0 if there is a \({\mathbb{1}}\). Therefore, the columns carry the information of how the generators act on individual qubits. The generators of two check matrices C1 = (A1∣B1) and C2 = (A2∣B2) commute if and only if
However, the parity check matrix does not carry all the information about S, since the signs of the generators are not included in C. To keep track of the signs, we add an extra column ω to C such that C = (A∣B∣ω), where ωi = 0 if gi is positive and ωi = 1 if negative.
We recall that elementary row operations modulo 2 on the check matrix leave the stabilizer invariant: the multiplication of generators corresponds to the addition of the respective rows, and the multiplication and relabeling of generators does not affect S. It is important to remark that the multiplication of generators may change signs in ω, e.g., (X ⊗ X)(Z ⊗ Z) = − Y ⊗ Y. How the signs of the generators change is discussed in Section I of the supplementary material.
Graph states constitute a particular case of pure stabilizer states. These are defined by a graph of m vertices connected by edges \(e \in {\rm{E}}\). The generator associated with the vertex i appearing in Eq. (3) is
where the neighborhood N(i) is the set of vertices j connected to vertex i by an edge. For a graph state, the check matrix reads \(({\mathbb{1}}| \Gamma )\) where Γ is the adjacency matrix, representing the interaction between the qubits, and the phase vector is trivial ω = 0. An equivalent way to define a graph state is via controlled-Z gates CZuv = diag(1, 1, 1, − 1) acting on qubits u and v as
Clifford operations are the unitaries that keep the Pauli group invariant under conjugation. An important example is the one-qubit Hadamard gate H which acts as HXH† = Z, HZH† = X and HYH† = − Y. It is known that all qubit stabilizer states are graph states up to local Clifford operations (LC)35,36. Many of the currently known AME states are graph states up to LC, with the notable exception of the recently discovered four-quhex AME state37.
Holographic graph state
Here we aim to find a suitable graph state \(\left\vert {G}^{{{{\rm{opt}}}}}\right\rangle\) for experimental purposes which corresponds to the holographic state \(\left\vert H\right\rangle\) and to the tensor network in Fig. 2a respectively.
An index contraction corresponds to projecting the tensor onto the Bell state and performing a partial trace. This fact can be seen from Eq. (7) by defining an arbitrary state on m qubits and a projector \({P}^{+}=\vert {\phi }^{+}\rangle \langle {\phi }^{+}\vert \otimes {{\mathbb{1}}}^{\otimes m-2}\) with \(\vert {\phi }^{+}\rangle ={\sum \nolimits_{r = 0}^{1}}\vert rr\rangle\) the (unnormalized) Bell state,
Here, \(\vert \chi \rangle\) is the state after the index contraction. Note that the Bell state is a stabilizer state. Therefore, in case of \(\vert \psi \rangle\) being a stabilizer state, so will \(\vert \chi \rangle\) (see ref. 38,Section 2). That can be seen in more details in Section I of the supplementary information where a method to obtain the generators of \(\vert \chi \rangle\) is found.
Our tensor network has the six-qubit AME state as a building block, which can be expressed as a stabilizer state (see its graph representation in Fig. 3). Using this fact the contraction of the hyperbolic pentagon code leads to a stabilizer state \(\left\vert H\right\rangle\).
The state \(\left\vert H\right\rangle\) can be transformed into a graph state \(\left\vert G\right\rangle\) through a local Clifford operator V that is composed of a layer of one-qubit Hadamard gates followed by a layer of Z gates,
This fact is shown in Section II of the supplementary information. The Hadamard gates transform the check matrix of \(\left\vert H\right\rangle\) to \(({\mathbb{1}}| \Gamma | \omega )\), which is, up to the phase vector ω, the check matrix of a graph state. The Z gates applied set ω = 0. Note that, from the set of local Clifford operations, we only required Hadamard gates to transform \(\left\vert H\right\rangle\) to a graph state, up to the signs of the generators. We emphasize that the contracted qubits are not part of the holographic state but are only needed to construct the encoding.
For a given graph state, there exist many other local unitary equivalent graphs. While not all local unitary equivalent graph states are local Clifford equivalent39,40, it significantly reduces the complexity of the problem by considering only the subset of local Clifford operations. To facilitate the implementation where the boundary qubits are located according to their position in the tensor network, we are interested in preparation protocols that require few interactions of shortest range only. In principle, a graph with such properties can be found by trying all possible mappings to a graph states, by applying local Clifford unitaries brute-force.
A more refined strategy relies on the algorithm from ref. 41: This algorithm allows to generate the set of LC-equivalent graph states on a small number of qubits. The algorithm results in graphs that are nonisomorphic to each other. Thus, exploring all LC-orbit requires to additionally permute the associated vertices followed by checking whether the permuted graph is LC equivalent to the original graph. In practice the following strategy appears useful: one explores the LC-orbit, chooses a graph with a few number of edges, and then further optimizes the range of interactions while making sure of LC equivalence to the original graph. We note however that these steps are computationally intensive: The number of permutations grow super-exponentially. Furthermore, while the exact scaling of the LC algorithm is unknown, the LC orbit might also become super-exponentially large for n ≥ 1241.
For obtaining the graph \(\left\vert {G}^{{{{\rm{opt}}}}}\right\rangle\) (shown in Fig. 1) we have limited ourselves to the following strategy: Exploring the LC-orbit for the graph in Fig. 5b with n = 16 took our desktop computer a few seconds. Then we permuted only the qubits which were part of the building blocks, and checked LC equivalence to the original graph. Here both the LC orbit and equivalence check were carried out with the library from ref. 41. Note that, while the number of its edges is minimal in the LC orbit, the interaction range of the resulting graph may be not. The LC orbit of a n = 22 instance of the holographic code corresponding to six pentagons can still be explored orbit in around 10 min.
However, larger instances seem to require a more heuristic strategy: Instead of exploring the LC-orbit, we then apply heuristically Hadamard gates to \(\left\vert H\right\rangle\) that result in graph states [see Eq. (8)]. Finally, Z gates can always be applied to set ω = 0. Thus they do not play an important role in the optimization. This last strategy seems to work better for symmetric instances of the hyperbolic pentagon code. Surprisingly, it also leads to the improved graph from Fig. 1. Section VIII from the supplementary information shows a larger instance resulting from contracting eleven AME states corresponding to n = 36 qubits.
Holographic graph code
Here we show how the holographic code can be understood as a graph code29,42. From the graph code and its representation as graph state \(\left\vert G\right\rangle\) [see Eq. (8)], we derive the logical basis states [see Eq. (2)]. We emphasize that the results in this section applies for any graph code, including \(\left\vert {G}^{{{{\rm{opt}}}}}\right\rangle\).
We recall that the check matrix of a graph state is described by \(({\mathbb{1}}| \Gamma )\). Since the holographic graph state \(\left\vert G\right\rangle\) is maximally entangled across \({{{\mathcal{B}}}}| \partial {{{\mathcal{B}}}}\), we can write its adjacency matrix as

where rank(B) = k, as shown in ref. 43,Section II. The n first columns of the X- and Z-part carry the information how the generators act on the boundary qubits and the remaining k columns describe how the generators act on the logical qubits. Here \({\Gamma }_{{{{\mathcal{B}}}}}\), \({\Gamma }_{\partial {{{\mathcal{B}}}}}\) and B represent the interactions within the bulk, within the boundary, and between bulk and boundary qubits respectively. The corresponding edge sets are \({E}_{{{{\mathcal{B}}}}}\), \({E}_{\partial {{{\mathcal{B}}}}}\), \({E}_{\partial {{{\mathcal{B}}}}| {{{\mathcal{B}}}}}\).
Similarly to \(\left\vert H\right\rangle\) from Eq. (2), the graph state \(\left\vert G\right\rangle\) from Eq. (9) can be written as
The basis elements of the code space \(\vert {G}_{{i}_{1}\ldots {i}_{k}}\rangle\) with i1, …, ik ∈ {0, 1} can be defined as
where \(\left\vert {G}_{0\ldots 0}\right\rangle\) is the logical zero state and \({\{{\bar{X}}_{r}\}}_{r = 1}^{k}\) are the logical \(\bar{X}\) gates,
Eqs. (11) and (12) are derived in Section III of the supplementary information.
Now, we want to find the remaining logical gates \({\{{\bar{Z}}_{r}\}}_{r = 1}^{k}\) and the generators of the code space \({\{{g}_{r}\}}_{r = 1}^{n-k}\). It is clear that the generators must commute with the logical gates since their action leaves the code space invariant. As they act on \(\partial {{{\mathcal{B}}}}\) only, we consider the boundary qubits of the check matrix Eq. (9) and write it as42,Section 4

such that rank(B2) = k. Here B is decomposed into two matrices B1, B2 and \({\Gamma }_{\partial {{{\mathcal{B}}}}}\) into three matrices Γ1, Γ2, Γ3.
Performing row operations on Eq. (13) leads to the generators of the code subspace \({{{{\mathcal{C}}}}}_{G}\) and the logical operators \(\bar{Z}\) and \(\bar{X}\). The result is given by

The proof of this result can be found in Section IV of the supplementary information.
It is important to remark that with the row operations needed to obtain Eq. (14), the phase vector can also change. This will also introduce additional signs [see Section IV of the supplementary information for details] to the logical \(\bar{Z}\) gates and the generators of the code space associated to \(\left\vert G\right\rangle\).
Encoding
We now describe how an arbitrary state is encoded into the holographic code. The layout of Fig. 2 contains k bulk and n boundary qubits. Given the logical gates and the generators for the code subspace [c.f. Eq. (14)], we provide a recipe to encode an arbitrary k-qubit bulk state into the boundary. This recipe is a modification of the encoding method from ref. 42 and can be found in more details in Section V from the supplementary information.
Define the controlled logical gates acting on bulk qubit j in \({{{\mathcal{B}}}}\) as
with \({\mathbb{1}}\), \(\bar{X}\), and \(\bar{Z}\) acting on the boundary space \(\partial {{{\mathcal{B}}}}\).
A bulk state \(\left\vert {\phi }_{{{{\rm{in}}}}}\right\rangle\) encodes into a boundary state \(\left\vert {\phi }_{{{{\rm{enc}}}}}\right\rangle\) via
where UG = U3U2U1 with
After a successful encoding the bulk degrees of freedom are left in the product state \({\left\vert +\right\rangle }^{\otimes k}\), as illustrated in Fig. 4.
The state \(\left\vert {\phi }_{{{{\rm{in}}}}}\right\rangle\) to be encoded is localized in the bulk, while the boundary qubits are in the product state \({\left\vert +\right\rangle }^{\otimes k}\). After performing the encoding unitary UG the information is mapped to the boundary state \(\left\vert {\phi }_{\rm{enc}}\right\rangle\) and with the bulk in a product state \({\left\vert +\right\rangle }^{\otimes k}\).
The unitary UG is decomposed into three unitaries. The gates in U1 take into account the interactions among boundary qubits and bulk qubits separately [\({\Gamma }_{\partial {{{\mathcal{B}}}}}\) and \({\Gamma }_{{{{\mathcal{B}}}}}\) from Eq. (9)]. They prepare the logical zero state and the phases of the logical states respectively. The gates in U2 take into account the interactions between bulk and boundary qubits [B from Eq. (9)], entangling the bulk computational basis with the logical boundary states. Finally, U3 is responsible for disentangling both systems with the information from the bulk transmitted to the boundary. Note that the conditional gates \({{{\rm{C}}}}{\bar{{{{\rm{X}}}}}}_{j}\) and \({{{\rm{C}}}}{\bar{{{{\rm{Z}}}}}}_{j}\) act between the qubit j in \({{{\mathcal{B}}}}\) and the boundary \(\partial {{{\mathcal{B}}}}\), a gate CZuv acts on two qubits u, v that are both in either \({{{\mathcal{B}}}}\) or \(\partial {{{\mathcal{B}}}}\) only.
Since the logical gates are composed by a tensor product of Pauli gates, we can decompose \({{{\rm{C}}}}{\bar{{{{\rm{X}}}}}}_{j}\) and \({{{\rm{C}}}}{\bar{{{{\rm{Z}}}}}}_{j}\) into a product of CXuv and CZuv gates. We can see that with an example. Define a controlled gate composed by Pauli gates:
One can decompose it as
This decomposition is useful since CX and CZ gates are realizable in many experimental platforms.
Partial decoding
The decoding abilities of the hyperbolic pentagon code are related to its geometry, which is induced by how the AME states are arranged in the tensor network. Their contraction yields the holographic state \(\left\vert H\right\rangle\), which represents an isometry TH that encodes k bulk qubits into n boundary qubits through Eq. (1).
To see how a bulk region can be recovered from its nearby boundary, we partition the bulk into two complementary regions E and F along a cut γ with associated boundary regions ∂E and ∂F, shown in Fig. 2a. To each tensor network leg crossed by the cut γ we associate a qubit. These qubits form the Hilbert space \({{{{\mathcal{H}}}}}_{\gamma }={({{\mathbb{C}}}^{2})}^{\otimes | \gamma | }\). If there exists an isometry from E ∪ γ to ∂E, then the quantum information stored in E can be recovered from ∂E. A way to check whether such isometry exists is through the method of tensor pushing11,Section 5.3. Such a partial isometry can be written as,
where \({\vert {h}_{{{{\bf{ij}}}}}\rangle }_{\partial E}\), forms an orthonormal basis of ∂E.
Given a bulk state that was encoded through the isometry TH, one can apply then a partial isometry \({T}_{{{{\rm{h}}}}}^{{\dagger} }\) on ∂E to recover the bulk region E. This follows from the fact that TH can be decomposed in terms of the elements hℓij from Th as,
where Rj is a tensor mapping from F to ∂F. This decomposition emerges from the tensor network illustrated in Fig. 2a. The isometry Th is constructed by the building blocks geometrically situated in E, which in turn are contracted by ∣γ∣ indices to the rest of the building blocks situated in F.
One sees that TH followed by \({T}_{{{{\rm{h}}}}}^{{\dagger} }\) acts as identity on E i.e.,
where we used that \({\sum }_{{{{\boldsymbol{\ell}}}}\in {{\mathbb{Z}}}_{2}^{| \partial E| }}{h}_{{{{\boldsymbol{\ell}} {\bf{{i}^{{\prime} }{j}^{{\prime}}} }}}}^{* }{h}_{{{{\boldsymbol{\ell}} {\bf{ij}}}}}={\delta }_{{{{{\bf{ii}}}}}^{{\prime}}}{\delta }_{{{{\bf{j{j}}}^{{\prime}}}}}\) because the elements \(\vert {h}_{{{{\bf{ij}}}}}\rangle\) form an orthonormal basis. Hence, Th recovers the bulk information of E from its nearby boundary ∂E.
The isometry Th can be represented as a quantum state \(\left\vert h\right\rangle \in {{{{\mathcal{H}}}}}_{E}\otimes {{{{\mathcal{H}}}}}_{\gamma }\otimes {{{{\mathcal{H}}}}}_{\partial E}\). This state is constructed by contracting six-qubit AME states from the regions E and ∂E only and it can be converted to a graph state \(\vert g\rangle\) via local Clifford operations W, such that \(\vert g\rangle =W\vert h\rangle\). Eqs. (16) and (17) allow to obtain the encoding and decoding gates Ug corresponding to \(\vert g\rangle\). As done with the full code \(\left\vert G\right\rangle\), it is practical to optimize this ”partial” graph code \(\vert g\rangle\) with respect to the range and number of gates.
Recall that \(\left\vert G\right\rangle =V\left\vert H\right\rangle\) and \(\vert g\rangle =W\vert h\rangle\), where W, V are composed of local Clifford gates. Then, the decoding gate Ug has to be corrected with corresponding local Clifford gates (see Section VI from the supplementary information),
where VE, V∂E, WE, W∂E contain the local Clifford gates of V and W having support on E and ∂E respectively. Here, \({\tilde{U}}_{{{{\rm{h}}}}}\) is the unitary operator that performs a partial decoding of a boundary state that was encoded via \(\left\vert G\right\rangle\).
Recall that the bulk decomposes as \({{{\mathcal{B}}}}=E\cup F\) and the boundary as \(\partial {{{\mathcal{B}}}}=\partial E\cup \partial F\). Then a state \(\vert {\phi }_{{{{\rm{enc}}}}}\rangle\) that was encoded through \(\left\vert G\right\rangle\),
can be partially decoded by \({\tilde{U}}_{{{{\rm{h}}}}}^{{\dagger} }\)
In particular, one can check that for this partially decoded state
holds. Consequently, all quantum information contained in E can be recovered from its nearby boundary ∂E, demonstrating holographic properties. Which other recovery regions are possible is studied in ref. 11,Section 5.3.
A holographic model on 12 qubits
Here we consider a small instance of the holographic code on 12 qubits that exhibits holographic properties and describe the experimental preparation of its logical states, its encoding, as well as the decoding procedures. We also show how to recover a bulk region from its nearby boundary. The methodology relies on the formulation of the hyperbolic pentagon (HaPPY) code11 as a stabilizer graph code derived in the previous sections.
This toy model consists of four connected pentagons, each representing a six-qubit absolutely maximally entangled state (AME), also known as perfect tensor, as illustrated in Fig. 5a. The toy model involves twelve boundary qubits, labeled by 1 to 12, and four bulk degrees of freedom labeled by A, B, C, D, thus requiring 16 qubits in total.
Contracting four perfect tensors as shown in (a) leads to a small instance of the holographic code. The contraction is mapped to the graph state from (b). This state can be thought of as an isometry that encodes the bulk qubits (red) into the boundary qubits (golden). Optimizing the range and the number of edges of the graph in Fig. 2b over local Clifford operations leads to the graph in Fig. 1.
The building block of the hyperbolic pentagon code is the six-qubit AME state, for which a highly symmetric graph state representation exists (c.f. Fig. 3)33. The contraction of four such states yields the stabilizer state \(\left\vert H\right\rangle\) which carries both information about the code subspace as well as about the encoding. The resulting \(\left\vert H\right\rangle\) can be transformed to a graph state \(\left\vert G\right\rangle\) by the application of a single layer of Hadamard gates and a subsequent layer of Z gates, as shown in Section II from the supplementary information. As \(\left\vert G\right\rangle\) requires many long-ranges CZ gates, it is useful to choose a local Clifford equivalent graph state that requires gates of shortest possible range. Here we choose the state \(\left\vert {G}^{{{{\rm{opt}}}}}\right\rangle\) that is shown in Fig. 1, which can be found by exploring the local Clifford orbit Fig. 6. This graph has no edges that cross the center and is rotational invariant.
The encoded state \(\left\vert {\phi }_{{{{\rm{enc}}}}}\right\rangle\) is localized on the boundary, and the bulk qubits on E and the qubits on the cut γ are in the product states \({\left\vert +\right\rangle }^{\otimes | E| }\) and \({\left\vert +\right\rangle }^{\otimes | \gamma | }\) respectively. The partial decoding unitary \({\widetilde{U}}_{{{{\rm{h}}}}}^{{\dagger} }\) transmits the information from the boundary region ∂E to E.
From the graph representation of the state \(\left\vert {G}^{{{{\rm{opt}}}}}\right\rangle\) as illustrated in Fig. 1, the logical zero state and the logical \(\bar{X}\) gates are extracted as follows: remove the red vertices (the bulk qubits) and their incident edges one obtain the logical state \(\left\vert {G}_{0000}^{{{{\rm{opt}}}}}\right\rangle\), corresponding to Eq. (12). This logical state is illustrated in Fig. 7. The logical \(\bar{X}\) gates, given through Eq. (12), are determined by the red edges Brs that connect the bulk with the boundary and read

While the logical \(\bar{X}\) gates can be extracted directly from the graph in Fig. 1, the logical \(\bar{Z}\) operator do not seem to have such simple graphical interpretation. However, they can be found in Eq. (14) and read
Note that the logical gates in Eqs. (27) and (28) preserve the same rotational symmetry as the graph (Fig. 1) from which they are extracted.
The logical state \(\left\vert {G}_{0000}^{{{{\rm{opt}}}}}\right\rangle\) of the 12 qubit hyperbolic pentagon code as derived from the graph state in Fig. 1.
The logical operators can be further simplified when multiplied by the code subspace generators. However, we lose the graphical interpretation of the logical \(\bar{X}\) gates. Similarly, the code subspace generators can be optimized by multiplying each other. This can reduce the number of gates used in this section even more (see Section VII from the supplementary information).
Preparing the logical states
We describe how the logical states can be prepared experimentally. Throughout we will use the labeling from Fig. 5a. One starts by preparing the logical zero state \(\left\vert {G}_{0000}^{{{{\rm{opt}}}}}\right\rangle\) that is illustrated in Fig. 7 and whose formula is given by Eq. (12). Prepare \({\left\vert +\right\rangle }^{\otimes 12}\) and apply controlled-Z gates between qubits \(u,v\in {{{{\rm{E}}}}}_{\partial {{{\mathcal{B}}}}}\),
Here \({{{{\rm{E}}}}}_{\partial {{{\mathcal{B}}}}}\) consists of the 28 boundary-to-boundary edges from Fig. 7,
With the logical zero state prepared, one can now obtain the remaining logical states by applying logical \(\bar{X}\) gates stated in Eq. (12).
Encoding circuit
In the following paragraphs we describe how to encode an arbitrary four-qubit bulk state into twelve boundary qubits. Eqs. (16) and (17) describe the associated encoding procedure for \(\left\vert {G}^{{{{\rm{opt}}}}}\right\rangle\). This yields the encoding unitary HG, which can be decomposed into three parts.
-
(1)
Unitary U1 prepares the logical zero state and introduces real phases to the logical states as shown in Eq. (11).
-
(2)
Unitary U2 entangles the logical states of the boundary with the computational basis of the bulk.
-
(3)
Unitary U3 decouples the bulk from the boundary, yielding the encoded state on the boundary.
Eq. (17) shows the general form of these unitaries, in particular they can be decomposed in terms of CX and CZ gates. For the graph in Fig. 1 they simplify as follows:
because our graph does not have interaction between bulk qubits \({{{{\rm{E}}}}}_{{{{\mathcal{B}}}}}=0\). The set \({{{{\rm{E}}}}}_{\partial {{{\mathcal{B}}}}}\) is given in Eq. (30).
Then, U2 can be written as
by decomposing the logical gates \({{{\rm{C}}}}\bar{{{{\rm{X}}}}}\) into two-qubit CZ gates according to Eq. (27). Here the set \({{{{\rm{E}}}}}_{\partial {{{\mathcal{B}}}}| {{{\mathcal{B}}}}}\) is given by
Finally, U3 reads
where the logical \({{{\rm{C}}}}\bar{{{{\rm{Z}}}}}\) gates are decomposed into CX and CZ gates according to Eq. (28). Here the sets Vj and Wj are given by
Given the three unitaries written as explicit quantum gates, we can proceed to encode a bulk state. Expand a general bulk state as
and prepare the 12 boundary qubits in \({\left\vert +\right\rangle }^{\otimes 12}\). The application of U1 [c.f. Eq. (31)] prepares the logical zero state \(\left\vert {G}_{0000}^{{{{\rm{opt}}}}}\right\rangle\) from Eq. (29) on the boundary,
The subsequent application of U2 [c.f. Eq. (32)] entangles the bulk with the boundary,
Finally, the gate U3 [see Eq. (34)] decouples the bulk from the boundary,
The encoded state is then
with the computational basis \(\left\vert abcd\right\rangle\) mapped to the logical basis \(\left\vert {G}_{abcd}^{{{{\rm{opt}}}}}\right\rangle\).
Partial decoding circuit
The graph code (Fig. 1) gives information on how to perform the encoding. However, it provides little intuition on realizing a partial decoding operation, i.e., recovering a part of the bulk from its nearby boundary. The geometry of the tensor network indicates what partial recovery processes are possible in general as discussed in ref. 11,Section 5.3.
For our toy model, Fig. 8 illustrates how to perform a partial recovery operation for a specific choice of bulk and boundary regions. Consider the specific cut γ from Fig. 8a which separates two regions: ∂E ∪ E and ∂F ∪ F, where E ∪ F are bulk qubits (red) and ∂E ∪ ∂F boundary qubits (gold). Further, we define the black qubits labeled by I, II and III as those associated to each tensor network leg crossed by the cut γ. The cut is placed in such a way that the two contracted AME states in Fig. 8b act as an isometry Th from E ∪ γ to ∂E. As shown in Eq. (22), one can use \({T}_{{{{\rm{h}}}}}^{{\dagger} }\) to recover the bulk qubits from E by only reading the boundary ∂E.
The isometry Th can be represented as a quantum state \(\left\vert h\right\rangle\) obtained by a contraction of two AME states in Fig. 8b. This state \(\left\vert h\right\rangle\) can also be mapped to a graph state by applying local Clifford operations. Again, this graph can be optimized with respect to the number of edges and locality leading to the state \(\left\vert g\right\rangle\) illustrated in Fig. 8c. Section VI from the supplementary information shows how to correct the \({U}_{g}^{{\dagger} }\) for this local Clifford optimized code.
The decoding procedure contains then the following steps:
-
1.
Apply the corresponding local Clifford before \({U}_{g}^{{\dagger} }\).
-
2.
Apply the same procedure as described in Encoding circuit, but for the graph \(\left\vert g\right\rangle\) and in a reverse order since \({U}_{g}^{{\dagger} }={U}_{3}^{{\dagger} }{U}_{2}^{{\dagger} }{U}_{1}^{{\dagger} }\).
-
3.
Apply the corresponding local Clifford after \({U}_{g}^{{\dagger} }\).
For the graphs \(\left\vert {G}^{{{{\rm{opt}}}}}\right\rangle\) and \(\left\vert g\right\rangle\) illustrated in Figs. 1 and 8c respectively, the unitary gate \({U}_{{{{\rm{g}}}}}^{{\dagger} }\) is modified and given by \({\widetilde{U}}_{{{{\rm{h}}}}}^{{\dagger} }={Z}_{B}{U}_{{{{\rm{g}}}}}^{{\dagger} }\) (see the end of Section VI from the supplementary information). First, \({U}_{3}^{{\dagger} }\) can be written as
where the gates \({{{\rm{C}}}}\bar{{{{\rm{Z}}}}}\) decompose into CX and CZ according to
In Eq. (41), the sets Ωj, Vj, Wj are given by
Note that since the logical \(\bar{Z}\) gates shown in Eq. (42) have extra phases, we need to introduce a new set of gates described by \({V}_{\omega }^{j}\). After expressing the logical \(\bar{Z}\) gates via X and Z and because of Y = iXZ, only ZI and ZIII will have extra phases.
Second, \({U}_{2}^{{\dagger} }\) can be written as
by decomposing \({{{\rm{C}}}}\bar{{{{\rm{X}}}}}\) into CZ gates according to Eq. (42). Here the set E∂E∣Eγ is given by
The last unitary \({U}_{1}^{{\dagger} }\) is
with the sets EEγ and E∂E given by
Starting from the encoded state \(\left\vert {\phi }_{{{{\rm{enc}}}}}\right\rangle\) we introduce five extra qubits, two red from the bulk region E and three black from the cut (Fig. 8b), such that
For our graphs \(\left\vert {G}^{{{{\rm{opt}}}}}\right\rangle\) and \(\left\vert g\right\rangle\), we need to apply local Clifford operations after \({U}_{{{{\rm{g}}}}}^{{\dagger} }\) and not before, since \({\widetilde{U}}_{{{{\rm{h}}}}}^{{\dagger} }={Z}_{B}{U}_{{{{\rm{g}}}}}^{{\dagger} }\). Therefore, apply \({U}_{{{{\rm{g}}}}}^{{\dagger} }={U}_{1}^{{\dagger} }{U}_{2}^{{\dagger} }{U}_{3}^{{\dagger} }\) to obtain
and apply ZB to obtain the decoded state,
The state \(\left\vert {\psi }_{{{{\rm{dec}}}}}\right\rangle\) has the same reduction on E as \(\left\vert {\phi }_{{{{\rm{in}}}}}\right\rangle\) [see Eq. (26)]. Thus the bulk information on E can be recovered from the state \(\left\vert {\psi }_{{{{\rm{dec}}}}}\right\rangle\) by only reading its nearby boundary ∂E. Thus the sequence of unitary gates Eqs. (49)–(50) realizes partial decoding from the encoded state and hence can be used to demonstrate holographic bulk reconstruction.
In summary, we need 12 qubits to prepare a code state, 16 qubits to encode an arbitrary state and 17 qubits to perform partial recovery.
A circuit to perform encoding followed by partial decoding can also be realized with 17 qubits, as shown in Fig. 9. The encoding needs 12 boundary qubits and 4 bulk qubits initialized in a product state and \(\left\vert {\phi }_{{{{\rm{in}}}}}\right\rangle\), respectively. The result of the encoding is a product state in the bulk and an encoded state in the boundary \(\left\vert {\phi }_{{{{\rm{enc}}}}}\right\rangle\). The partial decoding needs 12 qubits from the encoded state in the boundary, 2 qubits (A and B) from the bulk region E that we aim to recover and 3 qubits (I, II and III) from the cut γ. The remaining bulk qubits (C and D) can be recycled to act as qubits on the cut for the partial decoding. Fig. 9 shows how the qubits C and D are reused as I and II. Note that we still need an additional qubit III to perform the partial decoding; we introduce such a qubit in the center.
The bulk qubits A, B, C and D are encoded into the boundary qubits 1, …, 12. After encoding, we reuse the qubits C (now III) and D (now I) and add an extra qubit III to perform the partial decoding. This procedure recovers the bulk degrees of freedom A and B from the boundary given by the qubits 1 to 5.
We emphasize that the experimental setup in Fig. 9 describes the case of performing a partial decoding when we have previously performed a general encoding. For performing a partial decoding given a 12-qubit boundary state, we have to add 3 extra qubits as shown in Fig. 8b.
Experimental feasibility
For the implementation of the graph states presented in this work the ability to entangle arbitrary qubits is essential. In many state-of-the-art approaches, the interaction between qubits is local, which constrains the connectivity of the artificial quantum system. Hence, the long-range entangling gates have to be decomposed into local entangling gates which then increases the number of gates necessary to realize an equivalent circuit. However, several platforms are outstanding with their ability to generate non-local connectivity between qubits and hence allow to prepare the entangled graph states. Platforms which provide such connectivity are trapped ions44, Rydberg arrays24, (artificial) atoms coupled to a cavity23,45. In the case of trapped ions, the long-range interaction between two qubits can be achieved by either using the phonon degrees of freedom in an ion crystal46 or a shuttling approach47, i.e., moving the ions next to each other and then entangle them. Similarly, recent experimental progress in Rydberg atom arrays allow for entangling arbitrary pairs of atoms by shuttling the atoms, bringing two atoms next to each other and then entangle them by using the Rydberg blockade mechanism.
In the case of (artificial) atoms coupled to a cavity, the two typical platforms are superconducting qubits coupled to a microwave cavity or Rubidium atoms coupled to a cavity. In superconductor based platforms Josephson junctions are used to form an artificial two level system.45, whereas in the case of atomic systems one frequently uses internal states of the atom23. The range of the interaction can be engineered by exploiting that a photon can travel along a cavity, while the atoms are connected to the cavity. Controlling the coupling between the (artificial) atom and the cavity then allows to engineer long-range interactions.
In principle, all of these three systems trapped ions, Rydberg arrays or (artificial) atoms coupled to a cavity are able to perform arbitrary local unitary operations and one entangling operation between two arbitrary qubits, which is sufficient to perform arbitrary unitary operations between two qubits48. For example, Rydberg atom arrays recently demonstrated the generation of 12-qubit cluster state and a seven-qubit Steane code with related stabilizer measurements24. Similar results were achieved in ion trap setups, where for example a 7 qubit color code49 or a 9-qubit Bacon Shore code state50 were realized.
Reference 51 bench-marked a trapped-ion setup with single-qubit, two-qubit gate and measurement fidelity of 0.99994(3), 0.9981(3) and 0.9972(5), respectively. Using such a setup, we make a simple estimation of the state fidelity. The logical zero state is obtained with a fidelity of 0.947(8) from the gate sequence described in Eq. (29). Other approaches to prepare the logical zero state require non-destructive stabilizer measurements27 and result in a fidelity of 0.88(2). The state fidelity shows a significant advantage in preparing the logical zero state as a graph compared to stabilizer measurements. This estimation is developed with more details in Section VII of the supplementary information.
Related work
Reference 11,Section 5.7–8 already highlighted that the hyperbolic pentagon can be formulated in the stabilizer formalism. The work of ref. 19 then explored more explicitly the stabilizer formulation, taking advantage of index contractions formulated in terms of Bell state projections and obtaining corrections to the Ryu Takanayagi formula for entangled input states. The resulting codes are not yet optimized over local Clifford operations to reduce experimental requirements. Reference52 introduced the concatenation of quantum codes through their graph state representation. This method of concatenation is not directly applicable to a more general tensor network such as the hyperbolic pentagon code, as in this case more general index contractions are required.
Discussion
In this work we provided a systematic method to represent the hyperbolic pentagon (HaPPY) code as a stabilizer graph code. This allows to engineer as of now theoretical models of holography in artificial quantum systems. Interestingly, the formulation as a graph code applies to any code defined through a tensor network with stabilizer states as building blocks. Furthermore, the method is not restricted to qubits, but, with suitable generalizations, also applies to qudits in prime dimensions. This provides us with the tools to engineer other codes in the same manner, e.g., the holographic state30, holographic CSS codes53, and random stabilizer tensor networks5.
Regarding the scalability of our proposal, the local Clifford optimization as performed here is a limiting factor to find experimentally suitable formulations for larger instances of the hyperbolic pentagon code. However, an inspection of the building blocks graphs before the contraction can provide intuition on how the final contracted graph code might look like. Reducing the number of entangling gates and keeping them short range is crucial for current noisy intermediate-scale quantum (NISQ) devices.
Several open questions of interest remain. It is unclear whether the usage of symmetric building blocks always helps in reducing the local Clifford gate complexity for optimizing the number and range of edges. It is also an unknown whether there is an efficient iterative procedure to build a larger holographic graph layer by layer. Finally, it would be interesting to understand the advantages and disadvantages of experimentally implementing the hyperbolic pentagon code in prime dimensions.
Code availability
The code that supports the findings is available in https://github.com/ganglesmunne/Engineering_holography.
Change history
17 May 2024
A Correction to this paper has been published: https://doi.org/10.1038/s41534-024-00847-4
References
Maldacena, J. The large-N limit of superconformal field theories and supergravity. Int. J. Theor. Phys. 38, 1113–1133 (1999).
Jahn, A. & Eisert, J. Holographic tensor network models and quantum error correction: a topical review. Quantum Sci. Technol. 6, 033002 (2021).
Kohler, T. & Cubitt, T. Toy models of holographic duality between local Hamiltonians. J. High Energy Phys. 2019, 1–64 (2019).
Hayden, P. et al. Holographic duality from random tensor networks. J. High Energy Phys. 2016, 1–56 (2016).
Nezami, S. & Walter, M. Multipartite entanglement in stabilizer tensor networks. Phys. Rev. Lett. 125, 241602 (2020).
Vasseur, R., Potter, A. C., You, Y.-Z. & Ludwig, A. W. W. Entanglement transitions from holographic random tensor networks. Phys. Rev. B 100, 134203 (2019).
Chen, A., Ilan, R., de Juan, F., Pikulin, D. I. & Franz, M. Quantum holography in a graphene flake with an irregular boundary. Phys. Rev. Lett. 121, 036403 (2018).
Bienias, P., Boettcher, I., Belyansky, R., Kollár, A. J. & Gorshkov, A. V. Circuit quantum electrodynamics in hyperbolic space: from photon bound states to frustrated spin models. Phys. Rev. Lett. 128, 013601 (2022).
Kollár, A., Fitzpatrick, M. & Houck, A. Hyperbolic lattices in circuit quantum electrodynamics. Nature 571, 45–50 (2019).
Zhang, W., Yuan, H., Sun, N., Sun, H. & Zhang, X. Observation of novel topological states in hyperbolic lattices. Nat. Commun. 13, 2937 (2022).
Pastawski, F., Yoshida, B., Harlow, D. & Preskill, J. Holographic quantum error-correcting codes: toy models for the bulk/boundary correspondence. J. High Energy Phys. 2015, 1–55 (2015).
Harlow, D. The Ryu–Takayanagi formula from quantum error correction. Commun. Math. Phys. 354, 865–912 (2017).
Cao, C. J. & Lackey, B. Quantum lego: building quantum error correction codes from tensor networks. PRX Quantum 3, 020332 (2022).
Cree, S., Dolev, K., Calvera, V. & Williamson, D. J. Fault-tolerant logical gates in holographic stabilizer codes are severely restricted. PRX Quantum 2, 030337 (2021).
Bao, N., Cao, C. & Zhu, G. Deconfinement and error thresholds in holography. Phys. Rev. D 106, 046009 (2022).
Farrelly, T., Milicevic, N., Harris, R. J., McMahon, N. A. & Stace, T. M. Parallel decoding of multiple logical qubits in tensor-network codes. Phys. Rev. A 105, 052446 (2022).
Harris, R. J., Coupe, E., McMahon, N. A., Brennen, G. K. & Stace, T. M. Decoding holographic codes with an integer optimization decoder. Phys. Rev. A 102, 062417 (2020).
Bhattacharyya, A., Joshi, L. K. & Sundar, B. Quantum information scrambling: from holography to quantum simulators. Eur. Phys. J. C 82, 458 (2022).
Mazurek, P., Farkas, M., Grudka, A., Horodecki, M. & Studziński, M. Quantum error-correction codes and absolutely maximally entangled states. Phys. Rev. A 101, 042305 (2020).
Ebadi, S. et al. Quantum phases of matter on a 256-atom programmable quantum simulator. Nature 595, 227–232 (2021).
Arute, F. et al. Quantum supremacy using a programmable superconducting processor. Nature 574, 505–510 (2019).
Zhang, J. et al. Observation of a many-body dynamical phase transition with a 53-qubit quantum simulator. Nature 551, 601–604 (2017).
Periwal, A. et al. Programmable interactions and emergent geometry in an array of atom clouds. Nature 600, 630–635 (2021).
Bluvstein, D. et al. A quantum processor based on coherent transport of entangled atom arrays. Nature 604, 451–456 (2022).
Häffner, H., Roos, C. & Blatt, R. Quantum computing with trapped ions. Phys. Rep. 469, 155–203 (2008).
Monroe, C. et al. Programmable quantum simulations of spin systems with trapped ions. Rev. Mod. Phys. 93, 025001 (2021).
Abobeih, M. H. et al. Fault-tolerant operation of a logical qubit in a diamond quantum processor. Nature 606, 884–889 (2022).
Stricker, R. et al. Experimental single-setting quantum state tomography. PRX Quantum 3, 040310 (2022).
Schlingemann, D. & Werner, R. F. Quantum error-correcting codes associated with graphs. Phys. Rev. A 65, 012308 (2001).
Latorre, J. I. & Sierra, G. Holographic codes. Preprint at https://arxiv.org/abs/1502.06618 (2015).
Calderbank, A., Rains, E., Shor, P. & Sloane, N. Quantum error correction via codes over gf(4). IEEE Trans. Inf. Theory 44, 1369–1387 (1998).
Borras, A. et al. Multiqubit systems: highly entangled states and entanglement distribution. J. Phys. A Math. Theor. 40, 13407–13421 (2007).
Helwig, W. Absolutely maximally entangled qudit graph states. Preprint at https://arxiv.org/abs/1306.2879 (2013).
Nielsen, M. A. & Chuang, I. L. Quantum Computation and Quantum Information: 10th Anniversary Edition (Cambridge University Press, 2010).
Van den Nest, M., Dehaene, J. & De Moor, B. Graphical description of the action of local Clifford transformations on graph states. Phys. Rev. A 69, 022316 (2004).
Hein, M. et al. Entanglement in graph states and its applications. Proceedings of the International School of Physics "Enrico Fermi” vol. 162, 115–218. https://doi.org/10.3254/978-1-61499-018-5-115, https://ebooks.iospress.nl/DOI/10.3254/978-1-61499-018-5-115 (2006)..
Rather, S. A. et al. Thirty-six entangled officers of Euler: quantum solution to a classically impossible problem. Phys. Rev. Lett. 128, 080507 (2022).
Audenaert, K. M. R. & Plenio, M. B. Entanglement on mixed stabilizer states: normal forms and reduction procedures. New J. Phys. 7, 170–170 (2005).
Ji, Z., Chen, J., Wei, Z. & Ying, M. The LU-LC conjecture is false. Quantum Inf. Comput. 10, 97–108 (2010).
Tsimakuridze, N. & Gühne, O. Graph states and local unitary transformations beyond local Clifford operations. J. Phys. A Math. Theor. 50, 195302 (2017).
Adcock, J. C., Morley-Short, S., Dahlberg, A. & Silverstone, J. W. Mapping graph state orbits under local complementation. Quantum 4, 305 (2020).
Grassl, M. Variations on encoding circuits for stabilizer quantum codes. in Coding and Cryptology, (eds. Chee, Y. M. et al.), 142–158 (Springer Berlin Heidelberg, Berlin, Heidelberg, 2011).
Grassl, M., Klappenecker, A. & Rotteler, M. Graphs, quadratic forms, and quantum codes. IEEE Int. Symp. Inf. Theory - Proc., 45 (IEEE, 2002).
Ringbauer, M. et al. A universal qudit quantum processor with trapped ions. Nature 18, 1053–1057 (2022).
Devoret, M. H. & Schoelkopf, R. J. Superconducting Circuits for Quantum Information: an Outlook. Science 339, 1169–1174 (2013).
Porras, D. & Cirac, J. I. Effective quantum spin systems with trapped ions. Phys. Rev. Lett. 92, 207901 (2004).
Walther, A. Controlling fast transport of cold trapped ions. Phys. Rev. Lett. 109, 080501 (2012).
Lloyd, S. Almost any quantum logic gate is universal. Phys. Rev. Lett. 75, 346–349 (1995).
Nigg, D. et al. Quantum computations on a topologically encoded qubit. Science 345, 302–305 (2014).
Egan, L. et al. Fault-tolerant control of an error-corrected qubit. Nature 598, 281–286 (2021).
Quantinuum Announces Quantum Volume 4096 Achievement. Available at: accessed 14 April 2022); https://www.quantinuum.com/news/quantinuum-announces-quantum-volume-4096-achievement.
Beigi, S., Chuang, I., Grassl, M., Shor, P. & Zeng, B. Graph concatenation for quantum codes. J. Math. Phys. 52, 022201 (2011).
Harris, R. J., McMahon, N. A., Brennen, G. K. & Stace, T. M. Calderbank-Shor-Steane holographic quantum error-correcting codes. Phys. Rev. A 98, 052301 (2018).
Acknowledgements
We want to thank Máté Farkas, Michał Horodecki, Maciej Lewenstein, Pavel Popov, Anna Garcia Sala, Adam Burchardt, Martin Ringbauer, Markus Grassl and Karol Życzkowski for comments and fruitful discussions. G.A.M. and F.H. are supported by the Foundation for Polish Science through TEAM-NET (POIR.04.04.00-00-17C1/18-00). Much of this work was done while F.H. was working at the Jagiellonian University in Kraków. ICFO group acknowledges support from: ERC AdG NOQIA; MCIN/AEI (PGC2018-0910.13039/501100011033, CEX2019-000910-S/10.13039/501100011033, Plan National FIDEUA PID2019-106901GB-I00, Plan National STAMEENA PID2022-139099NB-I00 project funded by MCIN/AEI/10.13039/501100011033 and by the “European Union NextGenerationEU/PRTR” (PRTR-C17.I1), FPI); QUANTERA MAQS PCI2019-111828-2; QUANTERA DYNAMITE PCI2022-132919 (QuantERA II Programme co-funded by European Union’s Horizon 2020 program under Grant Agreement No 101017733), Ministry of Economic Affairs and Digital Transformation of the Spanish Government through the QUANTUM ENIA project call - Quantum Spain project, and by the European Union through the Recovery, Transformation, and Resilience Plan - NextGenerationEU within the framework of the Digital Spain 2026 Agenda; Fundació Cellex; Fundació Mir-Puig; Generalitat de Catalunya (European Social Fund FEDER and CERCA program, AGAUR Grant No. 2021 SGR 01452, QuantumCAT U16-011424, co-funded by ERDF Operational Program of Catalonia 2014-2020); Barcelona Supercomputing Center MareNostrum (FI-2023-1-0013); EU Quantum Flagship (PASQuanS2.1, 101113690); EU Horizon 2020 FET-OPEN OPTOlogic (Grant No 899794); EU Horizon Europe Program (Grant Agreement 101080086 — NeQST), ICFO Internal “QuantumGaudi” project; European Union’s Horizon 2020 program under the Marie Sklodowska-Curie grant agreement No 847648; “La Caixa” Junior Leaders fellowships, La Caixa” Foundation (ID 100010434): CF/BQ/PR23/11980043. Views and opinions expressed are, however, those of the author(s) only and do not necessarily reflect those of the European Union, European Commission, European Climate, Infrastructure and Environment Executive Agency (CINEA), or any other granting authority. Neither the European Union nor any granting authority can be held responsible for them.
Author information
Authors and Affiliations
Contributions
All authors contributed to the scientific process and the writing of the article. FH and VK developed the conception of the project and the main theoretical idea. GAM and FH mainly worked out the theoretical details, while GAM and VK specifically considered the experimental feasibility.
Corresponding author
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher’s note Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Supplementary information
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Anglès Munné, G., Kasper, V. & Huber, F. Engineering holography with stabilizer graph codes. npj Quantum Inf 10, 48 (2024). https://doi.org/10.1038/s41534-024-00822-z
Received:
Accepted:
Published:
DOI: https://doi.org/10.1038/s41534-024-00822-z